In today’s enterprise environment, it’s difficult to overstate the value of high-quality data.
Data has worked its way into nearly every aspect of enterprise decision-making. It informs operational efficiency, marketing strategies, and compliance success. It enables organizations to increase adoption and improve collaboration.
Before it can do any of these things, data needs to be interpreted in a cost-effective way. Enterprise-level organizations and their stakeholders need to agree upon a common, well-documented understanding of how data moves throughout the organization. This framework must also stipulate who has access to data and why.
Organizations that establish clear data governance policies set themselves up for highly streamlined operations, reliable profitability, and resilience against uncertainty. Over the past few years, data governance has become so important that many enterprises dedicate a C-suite position solely to managing and governing data.
This is a new phenomenon. Nearly 50% of publicly-traded companies with a Chief Data Officer appointed their first CDO between 2019 and 2022.
One of the primary responsibilities these executives have is establishing a data governance framework that enables enterprise data to generate value. They must then align people, processes, and technology to that framework in ways that help the organization achieve its strategic goals.
What Does a Well-Designed Data Governance Program Look Like?
Competitive enterprises must constantly gather feedback on day-to-day operations as well as long-term strategic initiatives. For a corporate data governance program to streamline this process, it must be established on multiple levels. A typical enterprise data governance system may include the following:
- A Governance Team. Since core governance directives are informed by executive strategy and insight, the governance team is often led by a C-suite executive. In some cases, a Director-level leader is provided with a department and charged with reporting to company executives.
- A Steering Committee. Data is embedded in nearly every aspect of daily operation, which means data governance must accommodate insights from many different sources. Steering committees are multi-disciplinary governing bodies that direct and prioritize data governance initiatives, while overseeing their execution.
- Operational Data Stewards. Data stewards are responsible for the management and oversight of organizational data assets. They coordinate policies and procedures to ensure data is accurate, consistent, complete, secure, and discoverable.
Accomplishing these goals requires a broad skill set that includes data architecture, data modeling, and information security. A comprehensive data governance program consists of 10 different components:
People
The success of any data governance initiative relies on the expertise and professionalism of the executive leaders, steering committees, and data stewards who execute it. Hiring top talent with demonstrable data governance expertise can make a significant difference in every aspect of the governance framework.
Strategy
High-level enterprise requirements must be comprehensively described in a strategic document that guides the governance roadmap. Establishing a strategic roadmap protects against scope creep and keeps the governance team focused on high-priority goals.
Processes
Data management processes include monitoring the quality of data, sharing analytics insights, and tracking data lineage, among many others. These processes are key to unlocking the value that enterprise data represents, and help inform policies that augment that value.
Policies
Data policies start with high-level statements declaring the expectations of data governance processes. They then inform lower-level operational guidelines about how individual users should treat data on a day-to-day basis. Policies are guided by security best practices and regulatory compliance, as well.
Standards
Documented, standardized processes keep “tribal knowledge” out of the data governance framework, ensuring everyone knows exactly how to format and communicate information effectively. ISO 3166 is an example of a popular, international data standard that specifies the definitions of country codes, as well as their dependent territories and other subdivisions.
Security
Data must be accessible to the people who need it, and inaccessible to those who don’t. Information security policies play an incredibly important role informing how governance policies differentiate between authorized and unauthorized users, and how suspicious activities should be handled.
Communication
Digital communication is a major element of data governance, but not the only one. Written and spoken communication also fall under governance frameworks, especially when considering sensitive data that requires additional security. Employees must know what format to use when communicating information, based on the context and sensitivity of the data being transmitted.
Integration
Organizational policies and structures should fit the overall framework established by data governance initiatives. Even internal office culture and water-cooler talk (or the lack thereof) must be taken into consideration when establishing new standards of behavior.
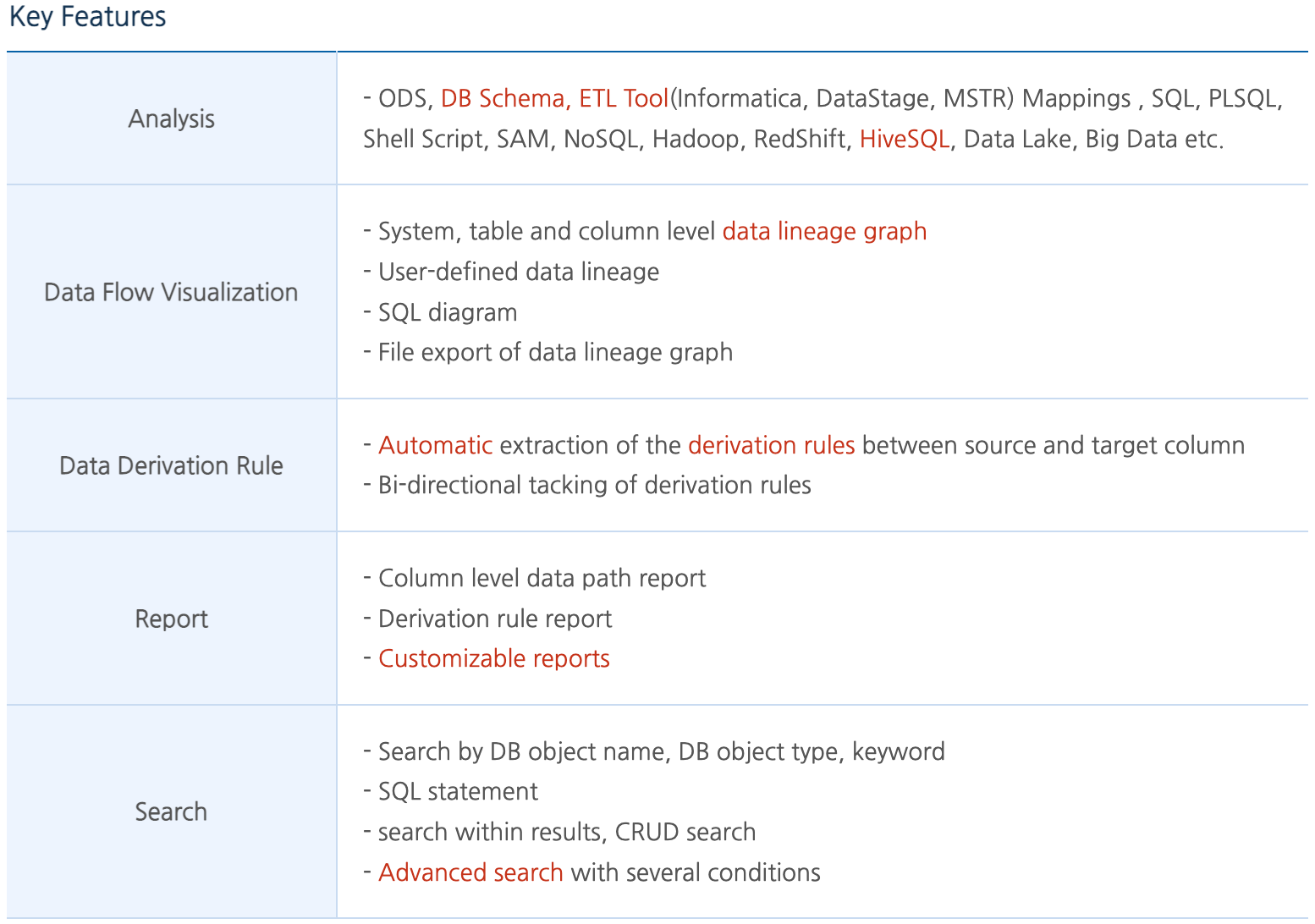
Analysis
To capture the value of data governance initiatives, leaders must analyze the right key performance indicators and business metrics. These are unique to each organization, but often include insights drawn from support tickets and security event logs, among other sources.
Technology
All data governance programs rely on various technologies to capture, manage, and analyze metadata in accordance with a governance framework. The larger and more complex the program is, the more robust its technology stack needs to be.
Each of these components has to work together smoothly in order to generate value with consistency in the enterprise environment. Poorly implemented data governance solutions can deeply impact the user experience for employees, customers, and business partners alike.
Managing the Flow of Data is Crucial to Effective Governance
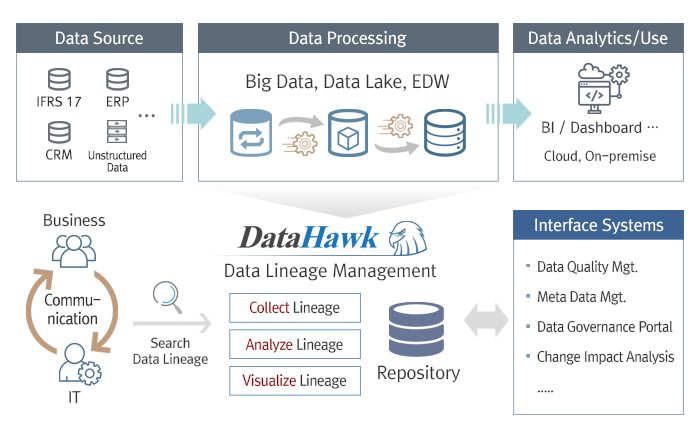
Many data governance technologies focus on establishing consistent, secure frameworks for managing data and reducing organizational silos. This is an important aspect of overall governance, but it only produces optimal results when combined with an optimized approach to controlling data flow throughout the organization as well.
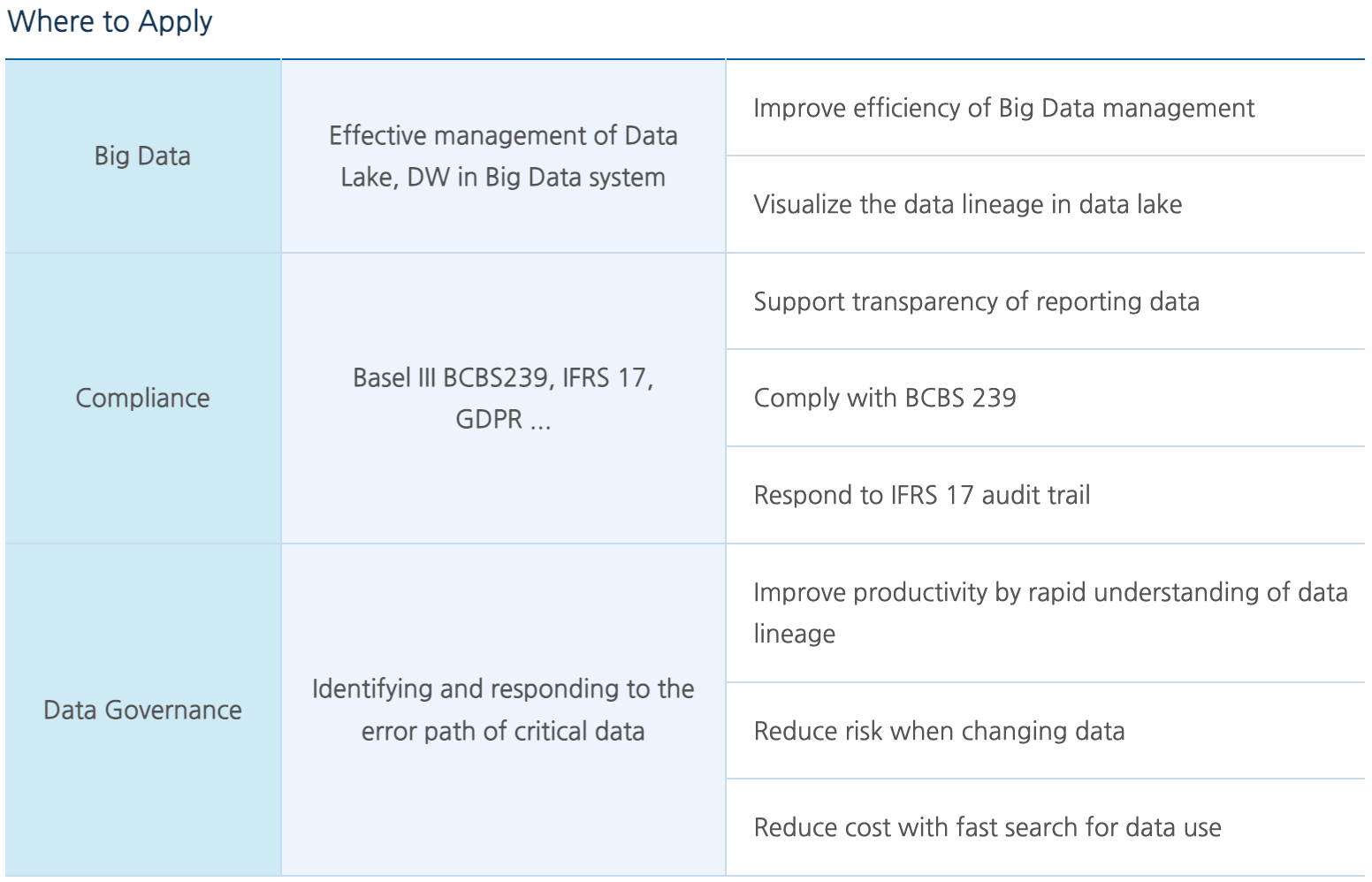
Data stewards and their governance partners need to be able to track the lineage of data as it travels through the organization. The ability to investigate how data arrives at its destination, and examine the processes that take it there are incredibly valuable for meeting information security and compliance objectives.
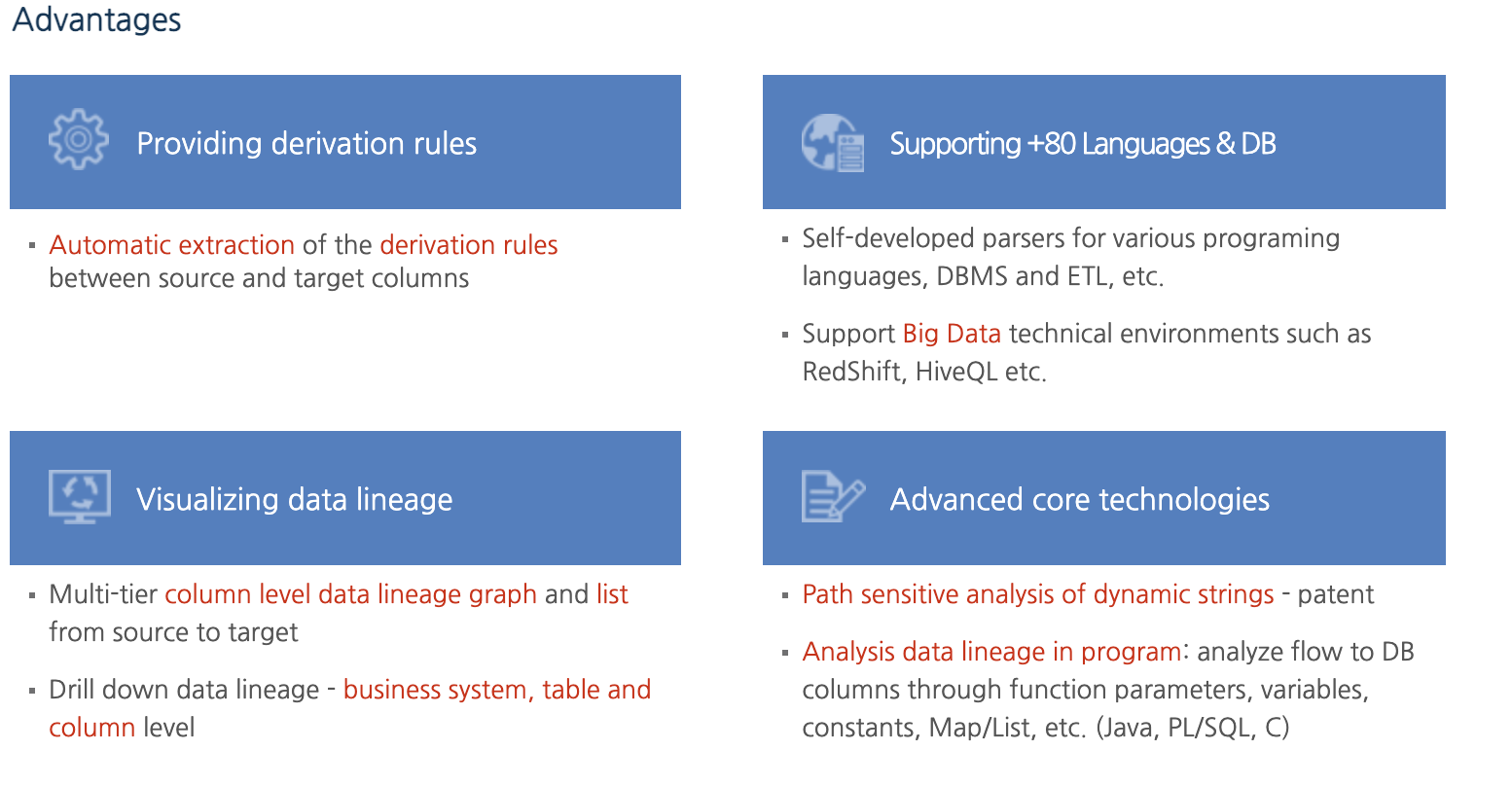
Enterprises and institutions that handle extremely high volumes of data throughput on a daily basis cannot adequately conduct these investigations in real-time without automated data lineage reporting. Data visualization solutions like DataHawk can help stewards, steering committee members, and executives gain visibility into how data flows throughout the organization and why.
Discover how to improve the efficiency and accuracy of your data lineage reports using a highly automated data governance platform with advanced search functionality. WeBridge provides governance technologies like DataHawk to enterprises that demand advanced, secure data lineage management solutions.